Cybersecurity protecting and securing your business data and network.
Data is the most valuable commodity in the world – and under threat every day. 1CONNECT can help you secure and protect your network infrastructure and data with leading edge cybersecurity solutions to suit every budget.
The threat to your business.
The business of today faces numerous threats to its cyber security which can compromise data and day to day operations.
In recent years we have seen many organisations become victims of ransomware attacks, massive data breaches, and supply chain threats with attackers being able to achieve many of their aims by using techniques that are not particularly advanced, blurring the distinction between nation states and criminals.
How to secure and protect your network
The Internet can be a hostile environment. The threat of attack is ever present as new vulnerabilities are released and commodity tools are produced to exploit them. Doing nothing is no longer an option. Protect your organisation and your reputation by establishing some basic cyber defences to ensure that your name is not added to the growing list of victims
Reducing your exposure to Cyber attack.
Fortunately, there are effective and affordable ways to reduce your organisation’s exposure to the more common types of cyber attack on systems that are exposed to the Internet. The following controls are contained in the Cyber Essentials, together with more information about how to implement them:
- Boundary firewalls and internet gateways - establish network perimeter defences, particularly web proxy, web filtering, content checking, and firewall policies to detect and block executable downloads, block access to known malicious domains and prevent users’ computers from communicating directly with the Internet
- Malware protection - establish and maintain malware defences to detect and respond to known attack code
- Patch management - patch known vulnerabilities with the latest version of the software, to prevent attacks which exploit software bugs.
- Whitelisting and execution control - prevent unknown software from being able to run or install itself, including AutoRun on USB and CD drives.
- Secure configuration - restrict the functionality of every device, operating system and application to the minimum needed for business to function.
- Password policy - ensure that an appropriate password policy is in place and followed.
- User access control - include limiting normal users’ execution permissions and enforcing the principle of least privilege.
As accredited partners for the world’s leading manufacturers of Firewall and security products, 1CONNECT can help you maintain the integrity of your valuable client information.
1CONNECT can help you find the right security solution whatever the size of your business and the requirements to protect it.
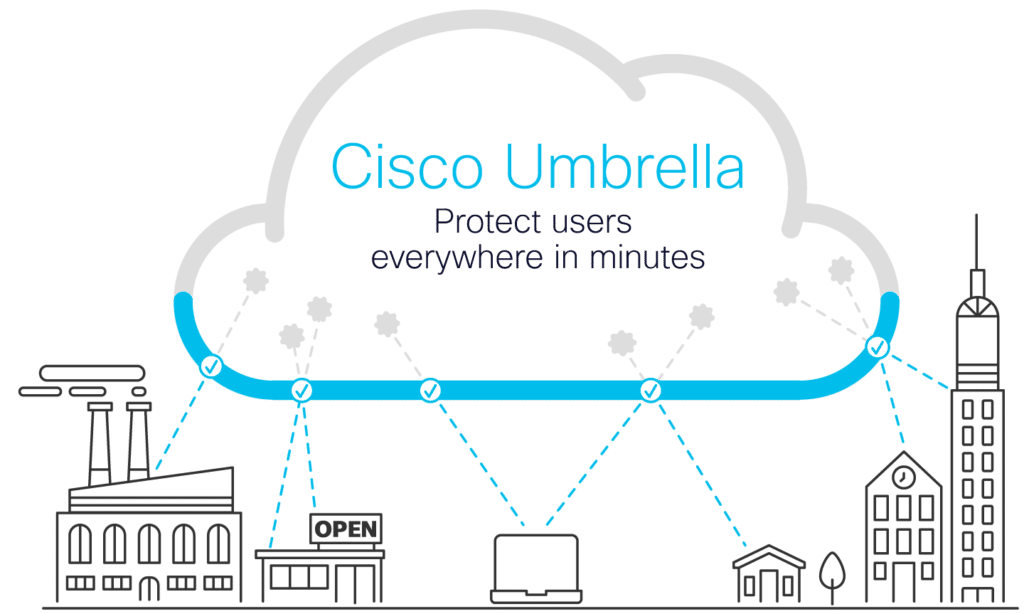
Cisco Umbrella
4 Key SASE benefits
Umbrella is the cloud-native, multi-function security service at the core of Cisco’s SASE architecture. It unifies firewall, secure web gateway, DNS-layer security, cloud access security broker (CASB), and threat intelligence solutions into a single cloud service to help businesses of all sizes secure their network. As more organisations embrace direct internet access, Umbrella makes it easy to extend protection to roaming users and branch offices.

Leveraging insights from Cisco Talos, one of the world’s largest commercial threat intelligence teams with more than 300 researchers, Umbrella uncovers and blocks a broad spectrum of malicious domains, IPs, URLs, and files that are being used in attacks. We also feed huge volumes of global internet activity into a combination of statistical and machine learning models to identify new attacks being staged on the internet.

Built into the foundation of the internet, Umbrella processes 220 billion internet requests for more than 20,000 businesses every day. By enforcing security at the DNS and IP layers, Umbrella blocks requests to malware, ransomware, phishing, and botnets before a connection is even established — before they reach your network or endpoints. The secure web gateway logs and inspects all web traffic for greater transparency, control, and protection. The cloud-delivered firewall helps to log and block traffic using IP, port, and protocol rules for consistent enforcement throughout your environment.

Umbrella categorises and retains all internet activity to simplify your investigation process and reduce incident response times. And, by using the Umbrella Investigate console and on-demand enrichment API, you have access to insights (historical and contextual) to prioritise incidents and speed up incident response. With Cisco SecureX (included with all Umbrella subscriptions) you can accelerate threat investigation and remediation by unifying Umbrella’s threat intelligence with other Cisco Security products, and your other security infrastructure. Automated response actions simplify security by eliminating manual tasks and stopping attacks earlier in the process.

1: Integrated security from the cloud
Umbrella is the cloud-native, multi-function security service at the core of Cisco’s SASE architecture. It unifies firewall, secure web gateway, DNS-layer security, cloud access security broker (CASB), and threat intelligence solutions into a single cloud service to help businesses of all sizes secure their network. As more organisations embrace direct internet access, Umbrella makes it easy to extend protection to roaming users and branch offices.
2: Better intelligence drives better security
Leveraging insights from Cisco Talos, one of the world’s largest commercial threat intelligence teams with more than 300 researchers, Umbrella uncovers and blocks a broad spectrum of malicious domains, IPs, URLs, and files that are being used in attacks. We also feed huge volumes of global internet activity into a combination of statistical and machine learning models to identify new attacks being staged on the internet.
3: Block malware easily
Built into the foundation of the internet, Umbrella processes 220 billion internet requests for more than 20,000 businesses every day. By enforcing security at the DNS and IP layers, Umbrella blocks requests to malware, ransomware, phishing, and botnets before a connection is even established — before they reach your network or endpoints. The secure web gateway logs and inspects all web traffic for greater transparency, control, and protection. The cloud-delivered firewall helps to log and block traffic using IP, port, and protocol rules for consistent enforcement throughout your environment.
4: Speed up and improve incident response
Umbrella categorises and retains all internet activity to simplify your investigation process and reduce incident response times. And, by using the Umbrella Investigate console and on-demand enrichment API, you have access to insights (historical and contextual) to prioritise incidents and speed up incident response. With Cisco SecureX (included with all Umbrella subscriptions) you can accelerate threat investigation and remediation by unifying Umbrella’s threat intelligence with other Cisco Security products, and your other security infrastructure. Automated response actions simplify security by eliminating manual tasks and stopping attacks earlier in the process.

Need more information?
Cisco Managed Firewalls
World-class security controls

Consistent policy and visibility

Integrate network and security
From your data center, branch offices, cloud environments, and everywhere in between, you can leverage the power of Cisco to turn your existing network infrastructure into an extension of your firewall solution, resulting in world class security controls everywhere you need them.
If your business is looking to invest in a Secure Managed Firewall appliance, giving you robust protections against even the most sophisticated threats without compromising performance when inspecting encrypted traffic, get in touch with 1Connect. We are an accredited Cisco partner and able to create a bespoke solution for your individual business security needs.

Free Security Product Trials
Cisco free product trials available direct from our online store.
This Is What We Do
This Is What They Say




Cyber Essentials
As accredited partners for the world’s leading manufacturers of Firewall and security products, 1CONNECT can help you maintain the integrity of your valuable client information.