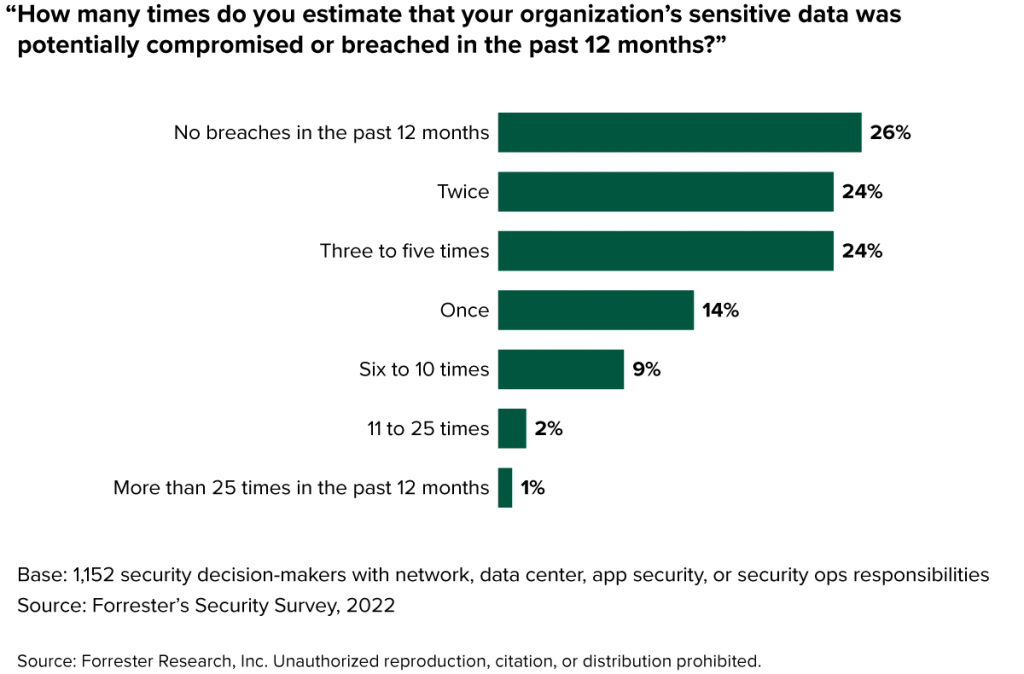
As routine as our morning brew and buttered toast, hearing of yet another cybersecurity event via mainstream news has become a daily norm. The 2022 Forrester’s Security Survey revealed a concerning figure: a staggering 74% of security decision-makers believed their organisation’s confidential data had been at risk or compromised within the preceding year (see Figure 1).
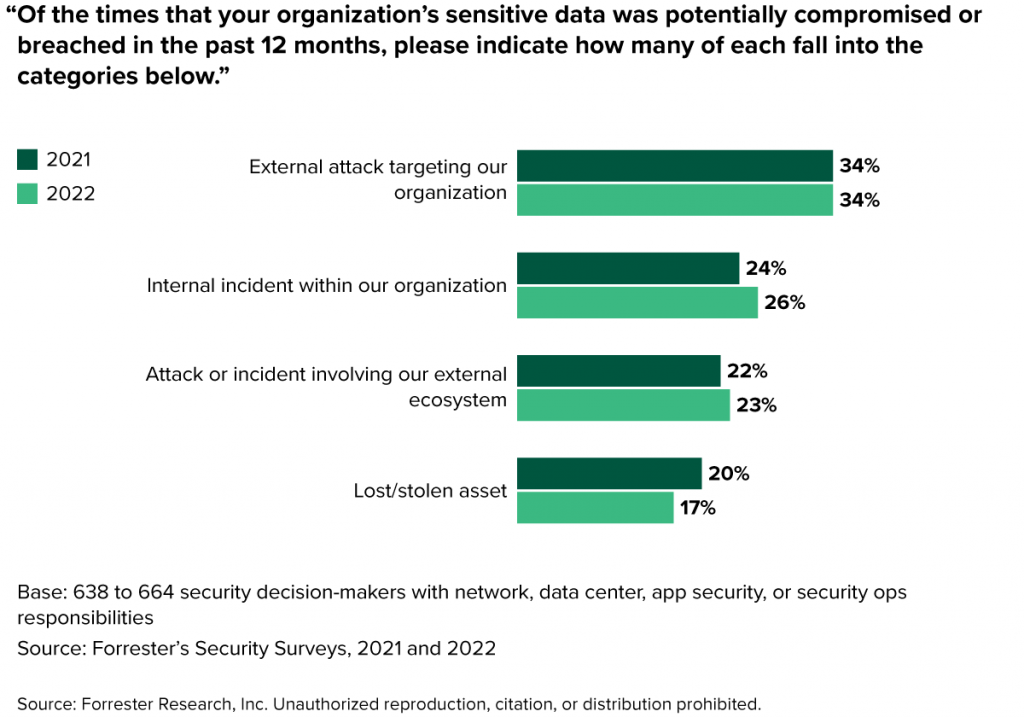
In terms of the nature of these security breaches, the patterns showed minimal deviation from 2021. While the proportion of external attacks remained stable, internal breaches, often termed as insider threats, saw a modest uptick, climbing from 24% to 26% (illustrated in Figure 2).
Yet, 2023 seems poised to bring a fresh set of challenges. With the advent of generative AI technologies, surging geopolitical tensions, and the complexities accompanying cloud technologies, the tactics employed by security squads are undergoing a transformation. They must now counter not just the well-known threats but also grapple with these new-age challenges (as depicted in Figure 3).
It’s imperative, therefore, for security and risk professionals to maintain their guard against the familiar risks, but they must also make provisions to mitigate threats posed by the latest technologies.